Table of Contents
- Certificate
- Dark fiber
- Digital Signature
- DMZ (Demilitarized Zone)
- DNS (Domain Name Server)
- Encryption
- Firewall
- IPsec
- Personal firewall
- PKI (Public Key Infrastructure)
- Private key
- Privileged user
- Public key
- Smart Card
- SSL (Secure Sockets Layer)
- Hardening
- TCP/IP or IP address
- VPN (Virtual Private Network)
- Vulnerability Assessment
Certificate

Many systems use digital certificates. These include web-based transactions (SSL or TLS); remote connectivity solutions (VPN’s), or full-blown PKI systems and their associated applications such as secure e-mail and database transactions.
- The certificate is used to publish (distribute) the public key of an individual or entity. The certificate contains the public key and the entity’s signature that is certifying that the key is valid.
- In the physical world, an official document bearing your signature (such as a passport or credit card) is a trusted document if it is signed by you and certified to be valid by the third party who issued that document.
- Certificates can be used in place of physical documents to establish a person’s identity or the identity of a computer system that they are connecting to.
- There are numerous applications for certificates, such as in e-commerce and remote connectivity. Like a physical piece of identification, you should only trust a certificate if you trust the third party who certified the public key and issued the certificate return to the top Certificate Authority – (CA).
- A certificate authority is a trusted third party that issues certificates containing public keys. If you have an understanding of what a public key is and how it is used, then you will realize that security is compromised if a user or server’s public key is forged or if conditions change that no longer make the owner of the public critical trustworthy.
- A certificate contains additional security information to prove that the key is valid and that it belongs to the person or entity named.
- The certificate authority certifies that this is true before putting their digital stamp of approval on it. The certificate can also be revoked by the CA.
- A certificate authority plays the role of a trusted third party in the same way that a credit card company certifies that a vendor can safely do business with the owner of a credit card or that the passport office certifies that you are who you say you are.
- The certificate authority must be known by the two parties and trusted by each of them for the certificates to be recognized as valid. Like a physical piece of identification, you should only trust a certificate if you trust the third party who certified the public key and issued the certificate.
- Some companies will perform their own CA function to issue certificated to employees as a means of authentication.
- Other organizations and individuals will rely on commercial Certificate Authorities such as Verisign or Entrust, for example.
![]()
Dark fiber
A secure network can be either a physical network made up of a wire strung between two systems or a virtual network VPN allowing multiple networks to share the same physical wire.
- Fiber optic cable is now becoming common as a transmission medium both within buildings and across long distances.
- The benefits are many when compared to the copper wire that it replaces. These include: Speed – higher transmission rates due to more efficient physics & Security – it does not act as an antenna as copper can do and is not as easy to tap into.
- Dark fiber simply refers to a fiber optic cable that has not been turned on. No light is passing through it, so it is said to be dark.
- A company would order dark fiber from their telecommunications supplier (telco) to connect two buildings if they wanted to hook their own transmission equipment to either end.
- Otherwise, the telecommunications company could provide a live network connection that includes telecommunications equipment managed by the telco.
![]()
Digital Signature

A digital signature is made up of two components: A hashing algorithm is applied to the document or data, resulting in a hash value uniquely representing the data.
- If the data is changed in any way, repeating the hashing process will have a different hash value.
- Otherwise, repeating the hashing process will yield the same results. The hash value is encrypted and sent along with the document so that the recipient can re-hash the document and compare the results to the original hash value.
- The encrypted hash value is referred to as a digital signature. For more information on how the signature is encrypted, see Asymmetric Encryption.
![]()
DMZ (Demilitarized Zone)

To isolate a corporate network from the Internet while allowing specific traffic to flow between the two, a DMZ can be set up.
- If the Internet is one network, and the corporate network is another, a DMZ is a third network connecting the two (sort of a digital no-man’s land).
- If you can imagine a castle with a moat, the land between the castle walls and the moat is no-mans-land or the castles DMZ during a battle.
- The only resources that would be physically located outside the castle walls but inside the moat require some defenses but can be sacrificed to keep the castle safe.
- In a corporate network, the DMZ is owned by the company so that the king of the castle owns the property surrounding the castle. The company’s web server can be located on the DMZ network.
- The web server is protected by a digital moat (a firewall), forming the company’s first line of defense.
- If an attack occurs and the hackers manage to cross the moat (get through the firewall), the webserver may perish like a peasant.
- Fortunately, a second more robust line of defense exists to protect the corporate network. A second firewall sits between the DMZ and the corporate network in the same way that the castle walls protect the castle’s occupants from the attackers who have managed to cross the moat.
- An effective DMZ is filled with all sorts of services available to the Internet and various obstacles such as firewalls to prevent theft or damage to the company’s public servers.
![]()
DNS (Domain Name Server)

Computers talk to each other using TCP/IP numbers (addresses), in the same way, that telephones contact each other using phone numbers.
- People have an easier time remembering names than numbers, so they exchange names when people are introduced.
- Later, if they want to call each other on the telephone, they can call directory assistance and get the phone number of the person they want to reach.
- You may want to reach a web site such as InfoCellar.com, but your computer needs to look up the proper TCP/IP address for the computer where the web site is located.
- A DNS is like directory-assistance for the Internet. In the same way that the phone company provides directory-assistance to find the number that enables you to connect to your friend’s telephone, a DNS provides your computer with the TCP/IP address of the webserver (or other services) that you are trying to connect to.
- So, when you try to reach my website, send an e-mail, or perform various network-related tasks, your computer does this by first querying a DNS to get the number. Then by using that number, it can connect to the webserver.
![]()
Encryption

Encryption refers to the process of scrambling data in a way that is almost impossible to unscramble by anyone but the intended recipient. (We can’t say it is impossible since given enough computing power and enough years. Eventually, every combination could be tried until the data was successfully unencrypted).
- An encryption algorithm is a mathematical equation or formula that is applied against the data to create a scrambled result. There are numerous encryption technologies such as DES, RSA, Diffie-Helman, and Blowfish, to name a few.
- The number of bits or “strength” of an encryption algorithm refers to an input value known as a key (see the public key or private key). Rather than keep the algorithm private, the algorithm is available to others who one might possibly ever want to do business with.
- What is kept secret is the input value or “key. ” The two primary uses for encryption are authentication (prove to me that you are who you say you are) and protecting (encrypting) data that is being transmitted or stored.
- Some encryption technologies and applications may use a symmetric algorithm, while others use asymmetric encryption algorithms.
- In other cases, both will be used in what is known as hybrid encryption technologies. For web security, SSL is an example of a hybrid technology that employs both methods.
- There are 2 standard encryption models in use: Symmetric encryption uses the same key to both encrypt and decrypt the data. Imagine that you agreed to loan me your car (ha! imagine). Since you are away on a trip, you have arranged to leave me a spare key.
- Symmetric key encryption works the same way. One key locks and unlocks the data, or a copy of that key can be used. If you also loan your car to three other people and get wrecked by the time you get home, you have no way of knowing who did it since we each have a copy of the same key. In hindsight, it would be much better if you bought three cars.
- Asymmetric encryption uses one key for encryption and another separate but related key for decryption. Asymmetric encryption supports two separate processes:
- Example 1: Authentication (you can prove that you are who you say you are) while technically this process is a bit more complicated than this example (in fact, the process is actually somewhat different), the following analogy works well in understanding the end result which is authentication. When you open a bank account, you are asked to provide your signature, which is then kept on file at the bank.
- Example-2: Protecting data (only accessible by the intended recipient) Your public key can be thought of as an open padlock for which you alone hold the key. A padlock could be used by me to lock up some data that I want only you to be able to get at. There is no risk in making the public key available to all. If a duplicate padlock existed and was publicly available to anyone, it could not be used to open the data that I secured. You alone hold the matching private key that opens the lock.
This process can be thought of as creating your public key (the signature on file) using your private key (your pen and hand movements, which are unique to you).
Later, when you write a check or make a withdrawal, you are asked to sign as a way of authenticating that you are who you say you are. The fresh signature (that only you can create) is unique to you and can be compared to the signature on file (that is available to everyone in the bank) to prove that you are who you say you are.
![]()
Firewall

In building construction, a firewall is quite simply a fireproof interior wall designed to stop the spread of flames from one part of the building to another.
- In network architecture, a firewall blocks the spread of viruses, hackers, and undesirable network traffic from one network to another.
- A firewall can be thought of as a black box joining two networks (a secure network and an unsecured network). In more robust network designs, two firewalls may be used (see DMZ).
- A network firewall may be a dedicated device purchased for this one purpose. It may be a service added to an existing network device.
- A simple network firewall can be created by configuring filters on the network router (a device that joins two networks).
- The traffic may be filtered based on the source or destination TCP/IP address, just like call blocking services filter out telephone calls from unwanted callers.
- A more sophisticated filter can allow traffic from any network address to pass, but only in support of specific applications (web traffic might be allowed while other application traffic can be blocked).
- An even more sophisticated firewall could be used to block the transmission of e-mail containing viruses or web pages containing bad words.
![]()
IPsec
IPsec is TCP/IP with security capabilities. IPsec can be thought of merely as an enhancement to the IP protocol, allowing it to provide security and authentication.
- While there are many uses for IPsec, it is often used to: provide a secure tunnel through the Internet that allows data to be passed securely between two computers; to authenticate a remote connection (to prove the identity of someone connecting to a corporate office over the Internet); to establish a VPN.
![]()
Personal firewall

A personal firewall performs the same sort of function as a network firewall. Instead of protecting an entire network, it protects an individual system, such as a home computer directly connected to a high-speed Internet connection.
- When Internet connectivity was over a phone line, network security wasn’t seen as crucial since the computer was only temporarily connected.
- While the window of opportunity for a hacker to strike was limited, there was still a risk.
- With high-speed networks, computers tend to be left connected for extended periods without supervision, making the system an easier target for hackers.
- A personal firewall is typically a software solution that filters traffic through the network connection.
- It can be configured to allow some or all applications to retrieve information from the Internet while preventing or allowing other applications from sending data to the Internet.
- For an example of how effective a personal firewall can be, install one on your system and watch the statistics that show how many attempts there are to access your computer.
- You will probably be amazed! In one case, a friend called to ask me if he should open up his firewall to let NOTEPAD. EXE access the Internet. Since notepad is not an Internet application, I told him that there is no reason that notepad. exe would try to access the Internet. Yet, his firewall kept asking him if it should be allowed.
- Turns out that notepad. exe was infected with a virus that he picked up by opening an infected e-mail message.
- Notepad had been replaced by an application that looked just like the original but had the added feature of acting as a server to allow a hacker to come and visit through the open door that is created.
- Usually, the attack would have been successful, but the correctly configured firewall detected and prevented it. Do you know what your notepad is doing?
![]()
PKI (Public Key Infrastructure)

Infrastructure describes the core components or the technological foundation upon which many business applications are built.
- Public key infrastructure is not a product but a term used to describe a combination of technologies that can be brought together to fulfill various security needs.
- In PKI, the infrastructure may be created to support a single business application. A much better return on investment can be achieved if it supports multiple security requirements and applications.
- Many standards exist within the various components that can be mixed and matched; selecting the best products and standards for your organization’s unique needs; Interoperability is between application and PKI components are not guaranteed, and technology doesn’t stand still, so select carefully.
- Components of a PKI include: A certificate server used by the CA to issues certificates; a certificate repository (a database that stores certificates); PKI client software to interact with the PKI infrastructure PKI server software to interact with the PKI infrastructure; encryption standards and protocols; consumers of certificates (e-mail clients, VPN endpoints, web servers, etc.).
- Additional components may include: Smart cards to store user’s private keys and a copy of their certificate that they can carry with them; Registration Authority servers that can handle pre-processing of the certificate requests; Backup Certificate servers, for load balancing or redundancy; People to perform all of the background checks that you deem necessary before certificates are granted;
- More people to manage the certificates, including revoking or issuing new ones. Executive Advice: It should be noted that it is possible to have secure applications that use certificates without the considerable investment required to build a Public Key Infrastructure. It simply means that several tasks or functions will not be automated.
- POINT: The value of a technology solution is often measured by the organization’s ability to respond quickly to a business need by having the foresight to invest in technology before it is needed.
- COUNTERPOINT: A sound business case will identify how well you can leverage your investment by ensuring that your PKI supports multiple strategic initiatives without becoming a dinosaur before you begin to use it.
![]()
Private key

A key is a unique number used as an input value by an encryption process. A private key is one part of a two-part security mechanism called asymmetric cryptography, which involves matching key pairs (private and public).
- In some cases, such as typical secure web transactions using SSL, the use of a private key is transparent to the user since web browser applications come with built-in key pairs.
- In that case, the key pairs allow the user to establish a secure connection but do not identify the users (users must type in a name and other credentials to be positively identified).
- In other applications such as VPN connections, or cases where private keys are used to positively identify a user to a secure web site, the user must first register their own private key with a certificate authority.
- Your private key is unique to you and must be kept confidential; If your private key is compromised, you can be impersonated;
- Private keys are often kept securely on a password protected “smart card” (See asymmetric cryptography then PKI for a more detailed description of this process).
![]()
Privileged user

A privileged user is simply a user who has an account on a computer, and that account has been assigning certain advanced privileges.
- On a Windows system, the ADMINISTRATOR has the highest level of privileges. On a Unix or Linux server, the account name is ROOT.
- Avoid surfing the Internet while logged on as someone with administrative rights.
- If you were to open an e-mail message containing a virus or access a web page and launch a malicious script, since this account has full access to your system and all of your hard drive, so does the script or virus.
![]()
Public key

A key is a unique number used as an input value by an encryption process. A public key is one part of a two-part security mechanism called asymmetric cryptography, which involves the use of matching key pairs (private and public).
- Typically when a user connects to a system that uses asymmetric cryptography (such as secure web transactions or VPN connection), the user is given the server’s certificate to prove its identity.
- The certificate contains the server’s public key. A public key is mathematically derived from your private key, that is how it is created. Your private key is kept private.
- Your public key can be given out to anyone that you want to without risk. Your public key is typically distributed in an electronic certificate. Your public key can be thought of as an open padlock for which you alone hold the key.
- A padlock could be used by me to lock up some data that I want only you to be able to get at.
- There is no risk in making the public key available to all. If a duplicate padlock existed and was publicly available to anyone, it could not be used to open the data that I secured.
- You alone hold the matching private key. See asymmetric cryptography then PKI for a more detailed description of this process.
![]()
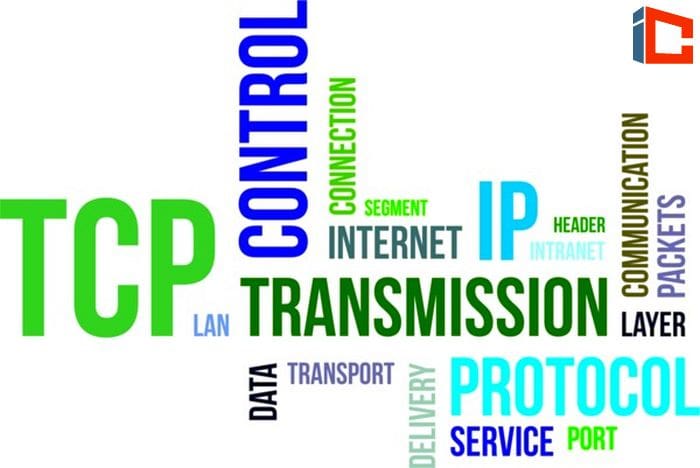
Smart Card
A smart card has traditionally meant a device similar to a credit card with a computer chip on it.
- A smart card is often used to physically store and transport an individual’s credentials, in the form of private keys and certificates.
- A smart card can be used to logon to a computer that the user has privileges on, providing the computer has a smart card reader.
- Smart cards can store data; data can be password protected or encrypted on the smart card; smart cards provide a means of carrying your computer credentials or other important files with you.
![]()
SSL (Secure Sockets Layer)

The SSL Protocol provides web browsers a secure way to communicate with web servers.
- You can identify a secure connection by the address of the web page.Normal web pages begin with http://, which indicates that the standard hypertext transfer protocol is being used to transfer the web page to you.
- Secure web pages have an address that begins with https, which indicates that a secure http connection is being used.
- The small padlock icon located in the lower right corner of your Internet Explorer web browser.
- Clicking on this lock will bring up the server’s certificate information, which can be used to confirm the server’s true identity.
- When an SSL connection is established, the web browser and server exchange certificates and negotiate a secure, encrypted connection.
- See PKI for an additional description of how this connection is encrypted.
![]()
Hardening

Hardening is a step by step process of securely configuring a system (usually equipment but can also be software) to protect it against unauthorized access while also taking steps to make the system more reliable. Hardening is often used to describe making a firewall or other piece of security equipment more secure.
![]()
TCP/IP or IP address

TCP/IP is a suite of protocols, or what is referred to as a protocol stack. If you imagine that sending data over a computer network is like sending mail through the postal system, each layer has a specific job to do.
- If you want to send a letter to your friend, you would first write the letter on paper. This is like creating a request for a web page or composing an e-mail message.
- Next, you would write your friend’s address and your return address on the envelope and seal it up with the letter inside. You have just created an IP datagram.
- The TCP/IP protocol stack’s IP layer is like your envelope containing both the source and destination IP (network) address on the outside and the data inside the package (datagram).
- The IP address is what allows your datagram to be routed across the Internet, in the same way, that the mailing address of your friend allows your letter to be routed through the postal systems.
- If you want to guarantee that your letter is delivered, you can send it registered mail. TCP adds extra information to the datagram that both the sender and recipient can use to determine if the whole datagram was delivered or if something went wrong.
- If there was a problem, TCP attempts to guarantee your datagram’s delivery by retransmitting it if necessary.
- After several failed attempts, TCP will notify your application that there is a problem, and you will receive an error message. In short, your application (perhaps a web browser) talks to the TCP software on your computer.
- TCP does its part by adding its own information to your letter and then passes everything down the stack to IP so that a datagram can be created and delivered to the recipient (a web server, e-mail server, or other).
- Warning: TCP/IP does not provide security by itself. For that, you should look at IPsec.
![]()
VPN (Virtual Private Network)

A VPN is a secure connection over a public network. A VPN “endpoint” can either be a PC running VPN client or server software;
- A dedicated VPN gateway that accepts secure remote connection; a firewall that accepts secure remote connections; a network router with VPN capabilities.
- VPN’s are set up to support connectivity between Home offices and corporate networks over the Internet Corporate office and Branch office over the Internet, or a shared telco connection; Within a corporate office when additional privacy is required (such as an executive network over the corporate network.
- The features of a VPN are that connections; are authenticated (we know who is connecting, and we authorize or deny those connections); Data sent over the VPN is encrypted; the network devices appear to be on the same network.
- A VPN can be established using any number of secure protocols, although IPSEC is becoming most common.
- Note: VPN connections can be set up to just perform authentication or to also support encryption. See PKI for a further discussion of the encryption process.
![]()
Vulnerability Assessment

A vulnerability assessment is a procedure where each part of your computing infrastructure is analyzed for potential security weaknesses.
- Assessments typically turn up things such as Operating systems that do not have the latest security patches installed; Office computers with modems installed; User accounts with privilege levels set too high; Network devices that have not been properly configured Connections to other networks; The list above is by no means thorough.
- Even the fact that a database server is connected to a network can be considered a vulnerability.
- The decisions that must be made following a vulnerability assessment are, what is the appropriate level of risk, and what is the worst that could happen.
- Based on the assessment results and review, an action plan can be created, and proper security measures are implemented based on the organization’s risk tolerance.
![]()